Search This Blog
Tuesday 18 December 2012
Instagram and that free lunch
Now we still do not know for sure if this is an swoop to make Instagram the worlds largest stock photo supplier by default or just an over enthusiastic lawyer covering all the bases.
But lets say Facebook do want the IP on all those photos, they host them and you do not pay to host them with them. so what is the problem?
What I hear you say, they cannot sell my photos! I took those! They are my IP.
Well hang on, I bet a lot of people who host their photos or art work online do so using services like Instangram, Facebook, Flickr, etc. If you then use these services as an online portfolio then you will likely benefit from this either financially or socially. What recompense do the providers get from this?
Because these services are amazing and cost money, not your money, someone elses money. So we place little value on them in real terms, we just complain when the people who provide these services try to recoup some of their investment and try to make them a profitable enterprise.
If we want a world where we can share without this fear of our IP being owned then we should all follow the philosophy of WikiPedia and contribute to a free and open platform for all the world.
I think Twitter is awesome, but someone is paying for this and one day they will get fed up paying for it because I cannot see how we can make Twitter pay. If we do you will all leave anyway bleating on about adverts and how it ruined Twitter.
Well think about it, a free lunch has never existed and we all pay in one way or another. If you want that ideological Utopian world online then remember who provides what you class as that now and look to who really is trying to make it happen.
Rant over.
Tuesday 11 December 2012
Be There Routed IP addressing with a Cisco 1841 Router
Be There have started to change how they offer public IP addressing in 2012 and now offer correctly subnetted IP blocks. This does mean however that you have to change your configuration as the end user, this is how to change the configuration for a Cisco 1841 router.
DHCP on the ATM0/0/0.1 Interface
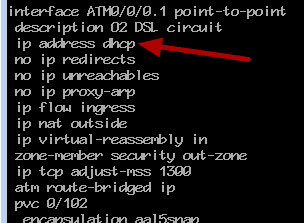
Be There have changed how you assign the IP address to the ATM interface, now this is assigned via DHCP and this IP address is not the IP that you will use for your site, this is the IP address that is used to provide the routed IP to you. So now you need to use the command
ip address dhcp
Zone Based Firewall and DHCP
Now the first issue you will run into is that the Zone Based Firewall is unlikely to be set to allow DHCP on the ATM interface. The ATM interface is going to be on your outside zone so we need to create two class maps to define the traffic as follows
1. ATM interface makes a DHCP request
2. ATM interface receives a DHCP reply
I have created two class maps for this, both contain a match for UDP ports 67 and 68
class-map type inspect match-any cmap-router-to-O2-dhcp
match protocol bootps
match protocol bootpc
exit
class-map type inspect match-any cmap-O2-dhcp-to-router
match protocol bootps
match protocol bootpc
exit
Policy Map
Once you have defined the class maps for DHCP you will need to allow the traffic into the router and out from the router, this involves the self zone and the outzone. DHCP traffic is a broadcast protocol so this is going to be sent over the PVC to the local Exchange and therefore we will not be inspecting this traffic, we need to pass this traffic in the Zone Based Firewall. Below I have my policy maps for Outzone to Self and Self to Outzone.
Outzone to Self
policy-map type inspect pmap-internet-to-router
class type inspect cmap-O2-dhcp-to-router
pass log
exit
class type inspect cmap-router-remote-access-protocols
inspect
This policy map inspects the traffic from Be There to the router and passes this and also logs this so I can see the traffic in the syslog to help in troubelshooting. The next inspection is my class map to allow SSH access to the router. You must here match the DHCP traffic first otherwise the ZBF will drop the traffic as not matching, ZBF rules are processed in order so you need to get your DHCP rule in first.
Self to Outzone
policy-map type inspect pmap-router-to-internet
class type inspect cmap-router-to-O2-dhcp
pass log
exit
class type inspect cmap-router-to-internet
inspect
exit
This policy map is the reverse and allows the router to send DHCP requests to Be There.
DHCP Process
![]()
Now when we shutdown the ATM0/0/0.1 Interface and the enable the interface a DHCP request will take place and this is shown above. You can see the ZBF passing the packets for DHCP in the log and that we have been assigned an IP addres on the ATM0/0/0.1 interface.
DHCP injected route
![]()
A new route is injected into the Cisco routing table for this circuit and this is shown in the config as a static route to the gwateway with a cost of 254. The cost of 254 is high so if you have another static router this will take precedence and this route will be used as the last resort.
Using your IP Block
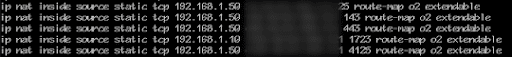
Your real routed IP block can now be used, this is achieved by configuring the Cisco to PAT out of the ATM0/0/0.1 Interface and this will use the first IP address in the block. For other services you can now create static NAT translations as shown above with one of the public IPs you have. This example is based on a Dual DSL router so these NAT translations will only function when the router has the default route to our Be There circuit.
Accessing the Router
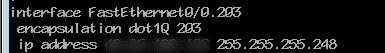
If you want to access the router via SSH for example you will need to know the DHCP IP address and this will change each time the ATM interface is enabled so it make sense to assign one of the public IP addresses to the router. This can be done by creating a sub interface on the Fast Ethernet interface and assigning this a new VLAN ID, this places this interface in its own VLAN and if we assign no ZBF zone then this will be seen as the SELF zone and the rules to and from this zone will apply.
Now you will be able to SSH to this IP address and the rules you have for Outzone to Self and Self to Outzone will apply.
Notification when a DSL Circuit does down
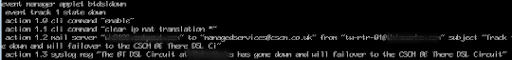
It is pretty handy to know if one of your DSL circuits is offline so you can use the IP SLA feature for this and track a ping to an IP out of one interface only, if the pring drops then you can then tell the router to clear the NAT translations and to inform you the circuit went down. I will not go into the full IP SLA here but for the notification you can use the event manager feature in Cisco Adavnced IOS.
Here you can see I have used event manager to note when my IP SLA Track 1 is down, when this occurs I can automatically clear the IP NAT translations and then send an email to our helpdesk to inform the team that the DSL circuit is offline.
Forgot that attachment in Outlook 2013?
We all forget things sometimes and nothing beats the forgotten attachment in an email. But now Outlook 2013 scans your email bosy and if it finds a reference to an attachment it reminds you that you havent attached one! Pretty simple but also pretty cool.
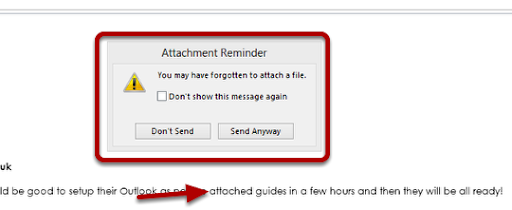
Outlook 2013 making sure I attach the PDFs I had forgotten!
Friday 7 December 2012
Citrix XenApp - How to configure failover Secure Access and STA
How to provide failover or multiple Secure Access Gateway Servers and STA for a Xen App 6.5 Farm
Secure Gateway Configuration Wizard
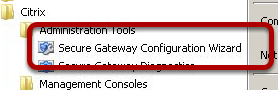
Open the Secure Gateway Configuration Wizard
Choose Advanced
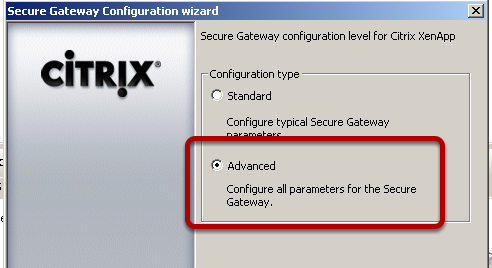
Select the Advanced option.
STA Servers
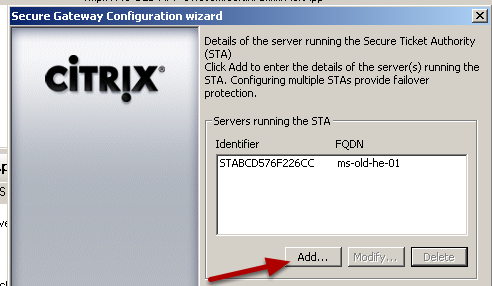
You now need to specify the servers that are acting as the STA in your XenApp Farm. Here I only have one server so I have a single point of failure so I am going to add a failover server.
Add STA Server

Enter the FQDN of your STA Server and the port you will communicate on, for simplicity I am using HTTP here.
Citrix Web Management
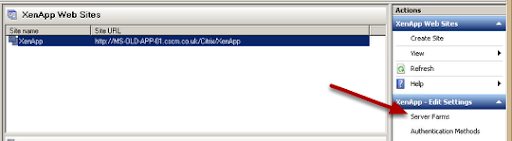
Now we need to use the Citirx Web Management application. Select the XenApp Farm and then choose Server Farms
Edit XenApp Farm
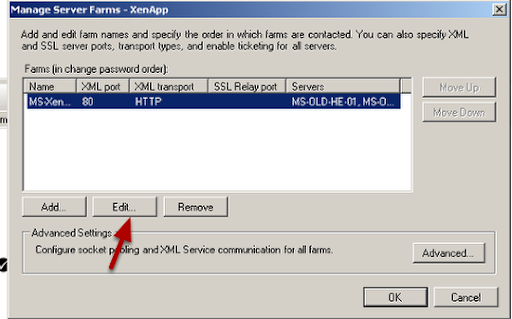
Select your XenApp Farm and then choose Edit
Add Failover Server
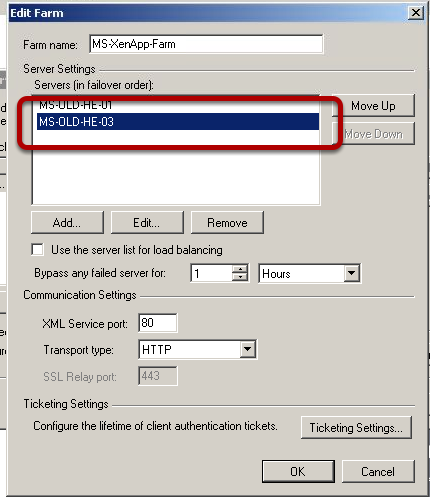
I now choose to add a XenApp Server, this will act as my failover server for authentication.
STA Settings
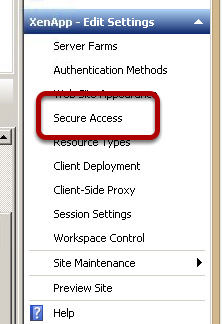
Now we need to specify the STA Settings for our Failover Server, choose the Secure Access option
STA Settings
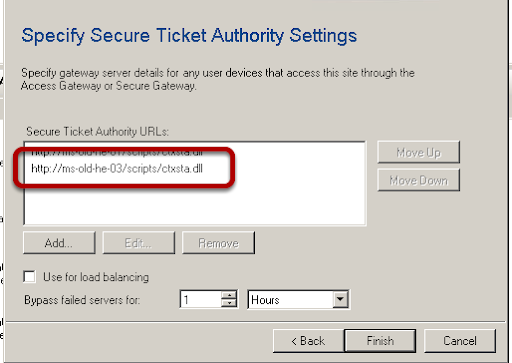
I now choose to add my Failover Server with the correct URL for STA https://servername/scripts/ctxsta.dll
Test Connection
You can now shutdown your original STA Server and then try to access a XenApp Server in your farm. This should now fail to find your Primary Server and then find your Failover Server for STA. This will take a little longer than a normal connection due to the need to check the Primary Server first.
Tuesday 4 December 2012
SQL Server - How to display only one Database to an account
For the purpose of a Hosted Service I needed to display a SQL database to a third party, I did not want to expose any databases except those for their client so I needed to find an approach.
SQL Server Databases

Here you can see that I have several databases on the SQL Server, the database I need to present to the third party is called Troy_Live
SQL Server Logins
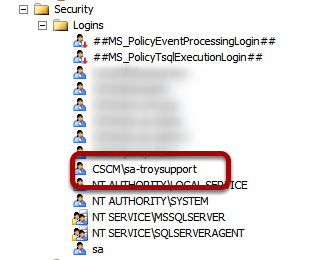
I have created a new SQL Server Login for the third party support to access the SQL Server Management Studio.
Access to SQL Server
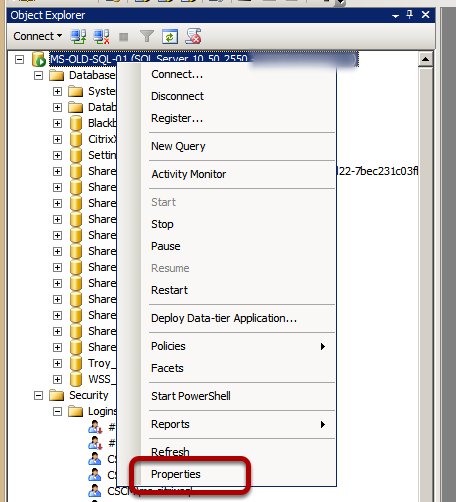
I will now change the access rights to the SQL Server for my support account, so on the root of the SQL Server right click and choose Properties.
Deny Access to View Any Database
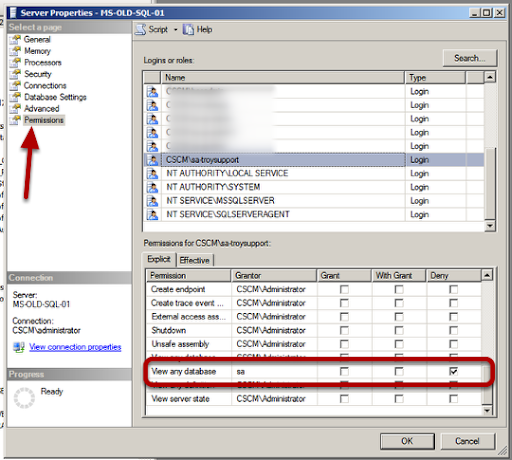
Select the pemissions option and then highlight your Security Login. You can now choose the permissions for this account and to hide all the databases from this account you need to choose the View any Database and set this to Deny
Set Permissions on Database you want to access
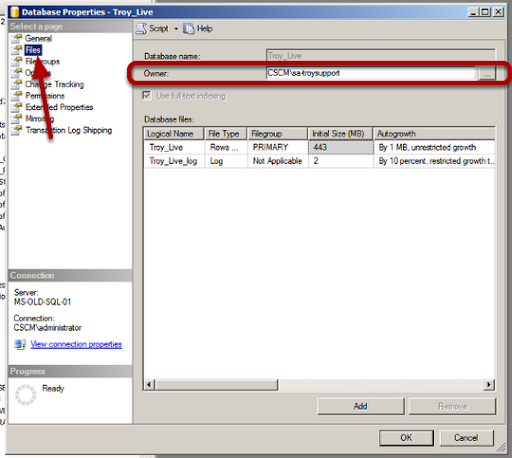
Now we have denied permisison to view all databases we need to allow acces to work on the correct database. Choose the properties of the database you want and then on the files option set the owner as the account you want to have access.
Logon as Support User
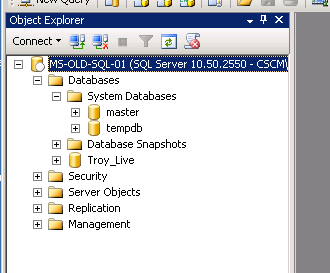
Now when I logon to the SQL Server Management Studio as my support user I can see only the database for my client and the master and tempdb databases.